Hello, I’m Keleis Andre, a cybersecurity expert. Today, I intend to discuss one of the fascinating topics in the realm of hacking: Wi-Fi Hacking. This field is trendy among hackers. Unfortunately, many people lack sufficient knowledge about attacks related to Wi-Fi networks, leaving them defenseless when faced with such threats. In this article, I’ll delve into one of the most recognized hacking attacks: DOS (Denial-of-Service) attacks, also known as deauthentication attacks in Wi-Fi networks.
What is a deauthentication attack on a Wi-Fi Network?
In a deauthentication attack, an attacker sends fraudulent packets to the Access Point and tries to disconnect all people connected to the modem or AP. This disconnection will continue until the DoS attack has stopped.
Why is a deauthentication attack carried out?
Why is a DoS attack carried out? Does the hacker want to prohibit a person’s connection to the Wi-Fi network? The answer could be both yes and no. Because people who are new to the world of hacking and security are likely to be curious and aimless and disconnect people from the modem.
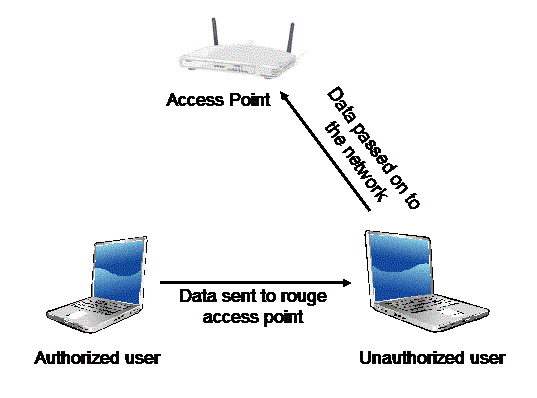
However, the primary purpose of this attack could be a much more dangerous event. One of these events could be obtaining a Handshake to hack your Wi-Fi password.
After the person is under attack when they try to reconnect to their Access Point, the attacker carries out a Sniffing attack on their Wi-Fi network and eavesdrops on the communications between them. Later, from the eavesdropped file (handshake), they can obtain the original Wi-Fi password.
How to carry out a Deauthentication attack
To carry out a DoS attack on a Wi-Fi network, a hacker needs a network card that supports monitoring mode. In the first step, they should put their WiFi adapter into monitor mode to scan the surrounding Wi-Fi networks and select their target Wi-Fi. After selecting the Bssid of their target, they can use it as follows:
To disconnect all users connected to the Wi-Fi network, they can use the following command:
aireplay-ng --deauth [number of packets] -a [Bssid] [Interface]
Ex: aireplay-ng –deauth 1000 -a 11:22:33:44:55:66 wlan0mon
To disconnect a specific person connected to the Wi-Fi network, they can use the following command:
aireplay-ng --deauth [number of packets] -a [Bssid] -c [target] [Interface]
Ex: aireplay-ng –deauth 1000 -a 11:22:33:44:55:66 -c 11:AA:22:33:44:BB wlan0mon
Dealing with DoS attacks on Wi-Fi networks
We should always adhere to the saying, “Prevention is better than cure”. So, it’s better to do the following to reduce attacks on Wi-Fi networks:
Use WPA2-PSK or WPA2-Enterprise encryptions.
- Always keep the firmware of our modem updated.
- Choose unpredictable and complex passwords for our Wi-Fi network.
- Set the Bssid name of our Wi-Fi network to Hidden mode.
- Limit the Wi-Fi signal to only be accessible in our usage area.
But even after doing the mentioned steps, we are still at risk. The only helpful thing to do when under a DoS attack is to turn off the AP or modem. Although it’s not an appropriate method, it can prevent damage to your device.




